
Security systems have fundamentally changed in recent years: what were once closed, hardware-centric isolated solutions have evolved into highly networked, software-based IT systems. Video surveillance, access control, and perimeter protection are now integral parts of IT infrastructure – and therefore exposed to the same threats as traditional IT systems.
With this development, the importance of audit logs* has increased significantly. Audit logs chronologically and tamper-proof document security-relevant activities, system events, and user actions. They are therefore a central tool for ensuring transparency, traceability, and control in increasingly complex security architectures.
New Attack Vectors – New Requirements for Evidence and Control
In addition to classic external threats such as malware, ransomware, APTs, or DDoS attacks, internal risks are moving further into focus. Authorized users in particular pose an increased risk. Administrators, maintenance personnel, or external service providers often have deep technical knowledge and extensive access rights. Manipulations may occur intentionally or unintentionally – and without appropriate mechanisms for evidence, they often remain undetected.
This is precisely where audit logs come into play – they close this gap. They document, for example, changes to configurations and parameters, access to live or archived video data, as well as user and role changes, system events, and software interventions. This turns a potentially invisible manipulation into a traceable action that, depending on the severity of the change, can also trigger a proactive alert.
Especially in cases involving insider threats or indirect attacks – for example through compromised credentials – audit logs are often the only reliable and robust source of evidence. Audit logs therefore form the basis for detecting threats from typical manipulation scenarios along the entire video chain – from the camera to data transmission to storage and display.
Audit Logs in the Context of Security by Design Axis consistently follows a Security-by-Design approach. Audit-log functions are an integral part of the Axis ecosystem – both at the device level and within the video management software. Combined with:
- user and role management
- certificate-based authentication (e.g., IEEE 802.1X)
- encryption (TLS)
- software and configuration monitoring
a security concept emerges that not only makes attacks more difficult but, above all, makes manipulations visible.
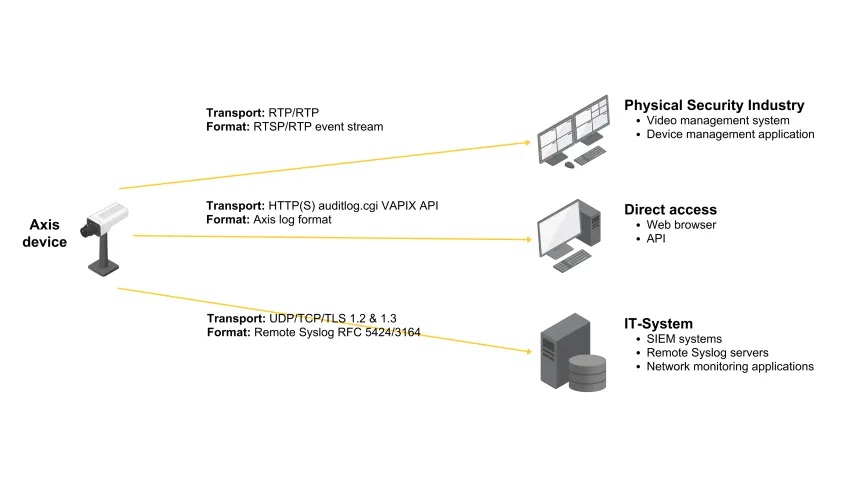
Audit logs can be accessed through various interfaces – for example via event streams to VMS systems, via HTTP/HTTPS using the VAPIX Audit Log API, or via remote syslog to central IT and SIEM platforms.
Audit Logs and Software Monitoring – Two Sides of the Same Coin
Modern security architectures increasingly rely on software monitoring (software sealing) to detect manipulations by authorized users. Audit logs form the operational foundation for this:
- detecting configuration changes
- triggering seal breaks
- integrating changes into clearly defined approval and workflow processes
Without audit logs, any software monitoring remains incomplete, as changes cannot be clearly attributed.
Regulatory Requirements: KRITIS, NIS2, ISO 27001
Audit logs are no longer a technical detail but a strategic element of modern security architectures. They play a crucial role in open, networked architectures where monitoring and tracking activities are essential to detect and prevent security incidents at an early stage. They are also indispensable for meeting increasing regulatory requirements – keyword: compliance – such as those defined by KRITIS, NIS2, and ISO 27001.
These regulations require comprehensive documentation and monitoring of system activities to ensure compliance and close potential security gaps. Furthermore, audit logs are of great importance when dealing with internal and privileged users. They help identify and prevent misuse and unauthorized access, thereby sustainably strengthening the internal security and integrity of systems.
Below are three application examples:
- Example 1:
- Example 2:
- Example 3:
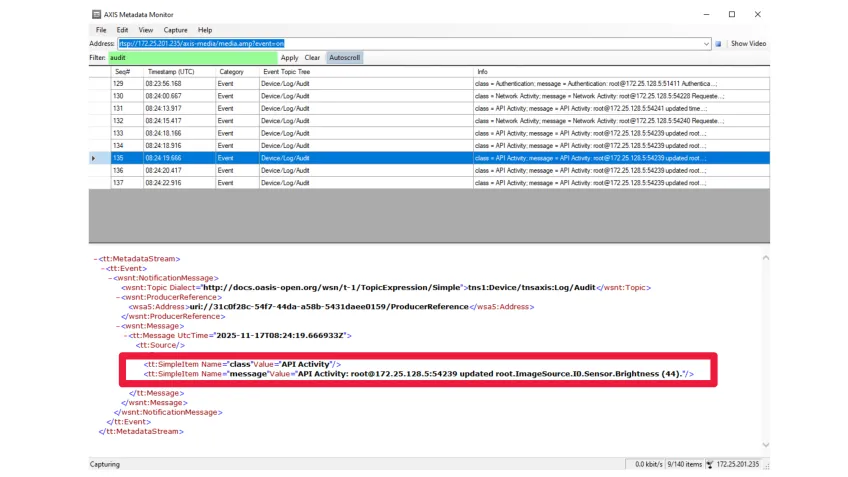
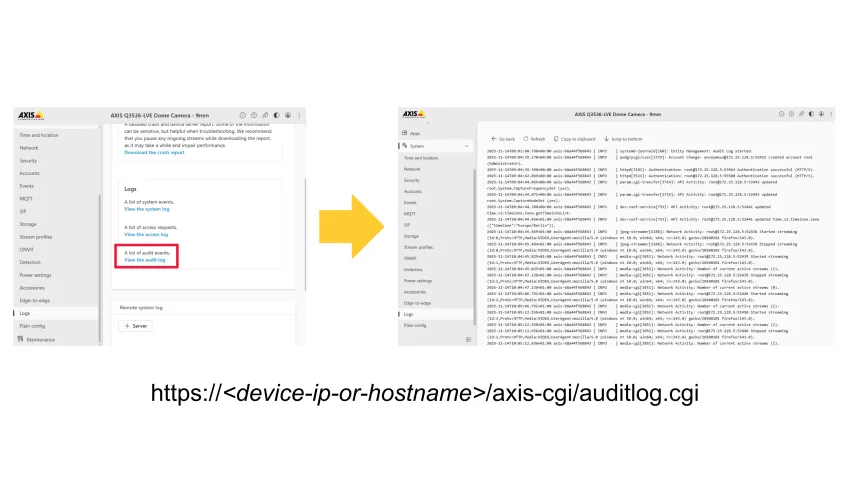
Axis devices offer diverse and flexible options for using audit logs – from real-time monitoring to long-term security analysis. Audit events can be integrated live into video and device management systems to respond directly to security-relevant activities. Additionally, the integrated web interface and the VAPIX Audit Log API enable direct access to logs for administrative reviews and targeted queries.
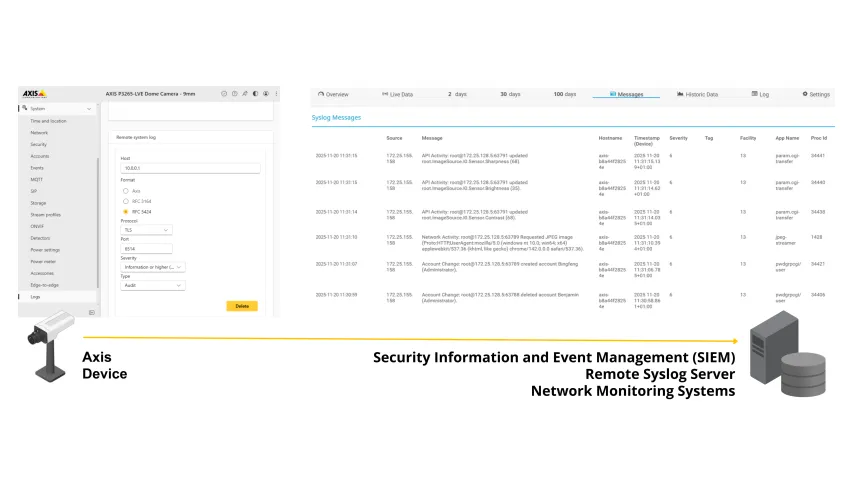
For scalable and audit-proof evaluation, audit logs can also be transmitted encrypted via remote syslog to central SIEM and monitoring platforms. There, they can be stored long-term, correlated, and effectively used for incident detection.
* Audit logs are immutable, chronological records of actions in IT systems that document who did what, when, where, and with what effect. They serve traceability, security, compliance, and forensic analysis.