Achieving maturity in the cybersecurity journey
6
minutes read
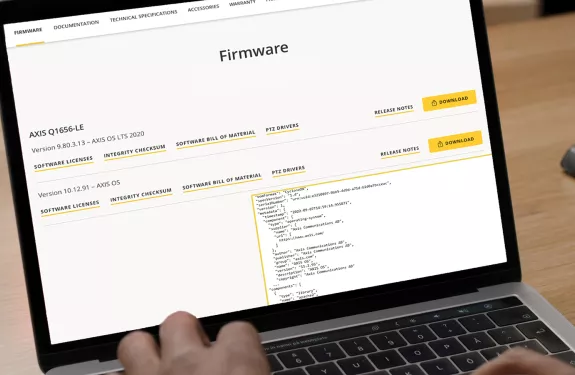
As technology advances, our commitment to cybersecurity strengthens. Together, we secure better cyber protection by providing you with the guidance, technologies, and tools you need to put safeguards in place.